You’ve heard about all of the breaches. You know no defense is impenetrable. And you’re likely aware of the risk that comes with storing payment card information.
Still, you need to process cardholder data to run your business—that much is unavoidable. So, how do you meet your operational needs while protecting your payment data and satisfying your regulatory compliance obligations?
By working with compliance and security experts, such as service providers and qualified security assessors (QSAs), you can ensure your organization is operating properly in regard to the PCI standards.
If your organization processes, stores, or transmits cardholder data, then the people, processes, and technology within your organization that interact or are exposed to payment card information are subject to the Payment Card Industry Data Security Standard (PCI DSS).
To comply, you’ll need to ensure your organization has the necessary security measures in place to sufficiently protect sensitive payment data.
In this post, we’ll review a few of the more prominent controls and provide you with a PCI compliance checklist for reducing scope and working toward PCI compliance solutions.
What is PCI DSS compliance?
The PCI DSS is an industry standard for securing cardholder data around the world. All organizations that process, store, or transmit cardholder data must adhere to the PCI DSS if they want to use cards from the major payment card brands that created and adopted the standard.
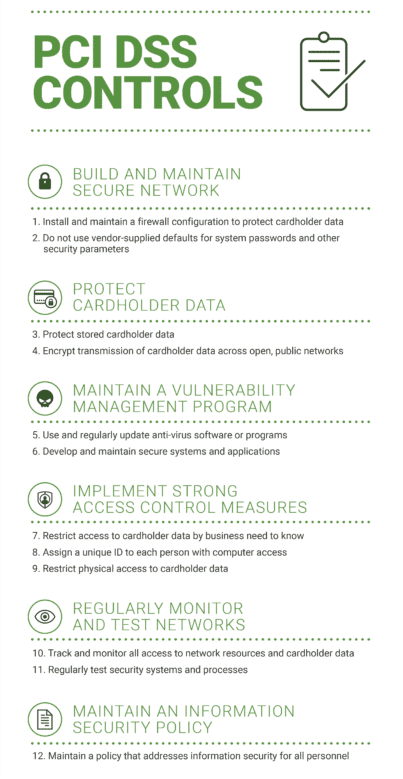
The PCI DSS consists of 12 requirements, or demands, each made up of several more specific, related controls for a grand total of more than 300 security checks. For example, PCI Requirement 1 covers the construction and maintenance of a secure network infrastructure. Meeting this overall requirement entails confirming the presence of properly secured firewalls, routers, and other applications to prevent unauthorized access to the cardholder data environment.
The 12 requirements fall under six overarching categories. These six categories provide an overview of the security controls required for PCI compliance. As essential as these individual concepts are, it’s important to remember that compliance and security are not the same thing. However, by prioritizing security—specifically a data-centric approach—compliance will likely follow.
Let’s build a PCI DSS compliance checklist by reviewing the six requirement categories of the PCI DSS.
PCI Security Checklist
1. Build and Maintain a Secure Network and Systems
This outlines requirements for network security. Specifically, it requires organizations to install and maintain firewalls and routers and not to use vendor-supplied defaults. All of the controls in this category are about securing your network and implementing proper network security mechanisms.
2. Protect Cardholder Data
This is a data security category. It’s concerned with the protection of the data elements themselves, regardless of their form. That could be data in storage, in transit, in processing, or even in physical forms, such as paper records like invoices or receipts. All of that data would be in scope, making tokenization and encryption appropriate measures for obfuscation.
3. Maintain a Vulnerability Management Program
This category is concerned with application security, so it details how an organization should protect its systems against malware, viruses, coding exploitations, and other items that affect application security. Potential solutions here could include antivirus software and security filters.
4. Implement Strong Access Control Measures
The first two requirements here address identity and access control measures. Identity refers to how to authenticate a user, and access control determines the user’s permission or access level to certain resources within your environment, specifically to cardholder data. The third aspect covers controls for physical access, such as requiring locks, cameras, etc., to prevent unauthorized physical access to a server room or data center.
5. Regularly Monitor Test Networks
This requirement is not so much concerned with implementing new security mechanisms as it is with maintaining your existing ones and ensuring they are sufficient. You need to be able to monitor your own network and detect security incidents if and when they occur. You also need to test your security systems and coding to ensure they are secure and functional, update and patch applications, and keep up with threat management for malware and viruses.
6. Maintain an Information Security Policy
This is essentially a policy that sets the tone for your entire organization’s information security strategy. It needs to address all of your employees and reflect your attitude toward PCI compliance and overall data security. This includes training programs and continuing education to ensure proper practices.
Now that we’ve established a list of high-level controls for PCI DSS compliance, let’s take a closer look at each of the 12 requirements and what it means.
PCI Standards Checklist
To help merchants, vendors, and other entities undertake the process of becoming PCI compliant, we created this overview of the PCI DSS’s primary requirements. This PCI compliance checklist was culled from the PCI SSC Quick Reference Guide.
PCI Compliance Checklist
Now that you have a general understanding of the categories and requirements of the PCI DSS, let’s look at each item under our PCI compliance checklist. We created this checklist based on the above security requirements, and we hope you’ll use it to see if your organization has the proper controls in place to protect cardholder data for PCI compliance.
If you’ve checked “yes” to each of these, your organization is well-positioned to succeed in your PCI compliance journey. However, this checklist is meant to provide only a basic overview of PCI compliant practices. It should not be considered an official or comprehensive checklist, nor a substitute for an attestation of compliance (AOC), report on compliance (ROC), or any other PCI compliance document or audit.
- Do you have a firewall or similar security measure in place to safeguard the system(s) in which you store, process, or transmit cardholder data?
- Is that firewall regularly updated and maintained?
- Have you replaced default passwords and vendor-supplied security parameters with unique and sufficiently strong alternatives?
- Are those passwords protected and safely stored to minimize their risk of exposure?
- Do you have sufficient security controls in place to protect cardholder data stored within your internal systems?
- Are you securing cardholder data when it is in transit?
- Are you at least using an approved method of encryption to protect it?
- Is it being protected when traveling across open networks?
- Does your organization have antivirus software or other virus-prevention programs?
- Is that software or program up to date?
- Do you have regularly scheduled reviews of that software to ensure that you always have the most recent version?
- Is your organization using the most recent version?
- Does your organization have secure systems and applications?
- Are those systems and applications being maintained?
- If not, do you plan to develop secure systems and applications in compliance with the PCI DSS?
- Is access to cardholder data restricted within your internal systems?
- Is this restricted access based on an individual’s need to know or need to handle that data to complete everyday tasks?
- Does the need to complete those tasks outweigh the risk of giving the individual(s) in question access to that data?
- Does every person within your organization have a unique user ID for computer access?
- Are those unique IDs enabled with permissions/access-control measures managed by a system administrator?
- Are those permissions/access controls consistent with business-need-to-know (e.g., marketing interns aren’t allowed to view the cardholder data of customers)?
- Does your organization restrict physical access to computers, servers, or other systems where cardholder data can be processed, stored, or transmitted?
- Do you have a system in place to log and monitor all visitors to facilities where cardholder data can be accessed?
- Is all media physically secured, safely stored, and not inappropriately distributed or accessible?
- Do you have a process for regularly reviewing your organization’s networks to prevent exploitation?
- Are these processes logged?
- Are these logs stored and secured to provide reliable audit trails?
- Are your systems frequently tested to discover any vulnerabilities?
- If vulnerabilities are discovered, are they being addressed and maintained over time?
- Do these tests occur any time new software is introduced or configurations are changed?
- Do these tests include internal and external network vulnerability scans and penetration testing at the required intervals?
- Are you monitoring critical system files to ensure they’re not illicitly accessed or modified?
- Does your company have an internal information security policy?
- Does this policy cover the requirements of the PCI DSS?
- Are those requirements being sufficiently addressed?
- Is your policy reviewed annually and/or whenever changes to your internal systems occur?
- Does this policy include measures for identifying and monitoring the PCI compliance responsibilities of service providers?
- Do you have an incident response plan that can be executed immediately in the instance of a breach?
Again, those questions are meant to provide an overview of the PCI DSS. The measure itself contains more than 300 controls, as opposed to the 40 or so covered here, but if you can answer yes to each of these questions, you’re likely in excellent shape for your upcoming PCI audit.
Tokenization for PCI Compliance
Many organizations use a combination of network segmentation and encryption, tokenization, or other obfuscation techniques to protect cardholder data in compliance with the PCI DSS. Each of these technologies offers its own set of pros and cons, but we find one security method to be exceptionally effective at reducing scope, minimizing risk, and simplifying PCI compliance—all while maximizing your data’s business utility, agility, and flexibility. This method is tokenization.
What are the risks of going all-in with processors?
For a stronger, simpler solution for PCI compliance, we recommend considering cloud-based tokenization. Tokenization captures payment card data before it even enters a merchant’s environment and then stores that data in a secure cloud offsite. This accomplishes two things: it saves businesses money by eliminating the need to pay for the hardware, software, and internal systems required to perform network segmentation, and it increases security by making data inaccessible to thieves and hackers. In the event of a breach, the only things to be compromised are worthless tokens that cannot be used by hackers to retrieve the corresponding sensitive data.
Additionally, by storing sensitive cardholder data outside of your environment, you effectively remove the systems that once housed that data from scope. This simplifies the compliance process and shifts much of the responsibility of validation to PCI compliance and security experts.
This superior functionality provides an exciting alternative for entities looking to more efficiently and easily operate within PCI standards. For a comprehensive look at PCI controls — and which ones are covered by TokenEx’s PCI tokenization solution—download our “PCI Compliance Guide” free ebook below.
Are you PCI compliant?
Read our ebook now to find out if you are compliant.